Cleaning viruses in the functions file on wordpress

Not so long ago, a virus appeared on many hosting, it is not entirely clear how he got them, but it is very likely that he got through one of the versions of WordPress. It is very important that before the update, aibolit and other scanners were not found and it could only be found by digging around with your hands. I managed to initially detect the virus by means of my hosting, which I have already spoken about more than once ukraine.com.ua. The built-in virus scanner on the hosting worked.
And then I started looking for viruses
After digging around on the Internet, I found a solution to the problem., I would like to share this solution with you.
If a strange code of this kind appeared on your site in the theme folder, then you were infected.
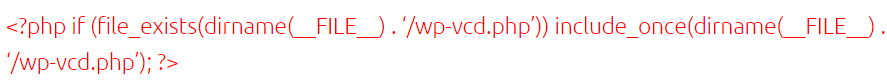
It was lucky for me, that a test site was infected on which I tested different plugins and I could experiment. The first thing I did, this removed the code in the file functions.php, it was placed at the top of the code, but it didn't have much effect., the next day i found a new code in the same place, and in all themes uploaded to the test site. In addition, it became clear, that not only this file is infected and it was necessary to dig further.
Next, I found a strange file in the WP core that was part of the wp-includes/class.wp.php virus, it was not in the base assembly and it appeared recently, therefore, this file could be deleted without fear and, by its name, search for files in which it could connect. Nearby, I found another wp-includes/wp-vcd.php file, it was also not from the kernel and was created exclusively by a virus.
It is important that not all sites where later I found viruses had these files, so maybe the virus was not the first version (mutated slowly), but in the functions.php file, the virus code was everywhere.
To make it easier for you to compare the core files, I left you a link to the official WP repository, on GitHub where you can see the list of files without downloading the full WordPress CMS package. Files can be viewed here: https://github.com/WordPress/WordPress/tree/master/wp-includes
I also found information that many people had strange code in the “wp-includes/post.php” file. Here is an example of the beginning of the malicious code:
![]()
The hackers included a virus file into this file.. You can see the standard view of an uninfected post.php file at the link https://github.com/WordPress/WordPress/blob/master/wp-includes/post.php.
It is important to check the functions.php file in all topics that are contained on your site. You can see the full listing of the virus here.: https://gist.github.com/alexandrpaliy/b3bb8a19433478fe32414895ad641709.
If you have such malicious code, it is important to remove it completely. In the example from the link above, the end of the virus is on 100 line.
I found some interesting information about this virus. People write that an additional user was created and even some had a hidden user, so don't forget to check the wp_users table for fake site admins.
Important! Don't forget to make a backup of your site's files and database before cleaning to avoid irreversible consequences..
Remember that many viruses are modified over time and you need to understand the code to clean them., as well as identify connections.
You can read about what viruses are and how you can deal with them in our article “How to remove a virus from a WordPress site“.
I can remove a virus from a WordPress site and set up protection for you
If it so happened that your site was infected or viruses appear all the time or its performance is impaired, then write to me and I will try to help you.
Mail: info@wp-admin.com.ua
/*

- Basic web design course;
- Site layout;
- General course on CMS WordPress and continuation of the course on template development;
- Website development in PHP.